User Oobe Create Elevated Object Server
On the server that Active Directory Domain Services (AD DS) runs on, open Active Directory Users and Computers by typing dsa.msc in the Run dialog, and then click OK. Click Users under your domain, and then do the following: If there's only one affected user, right-click the user, and then click Properties.

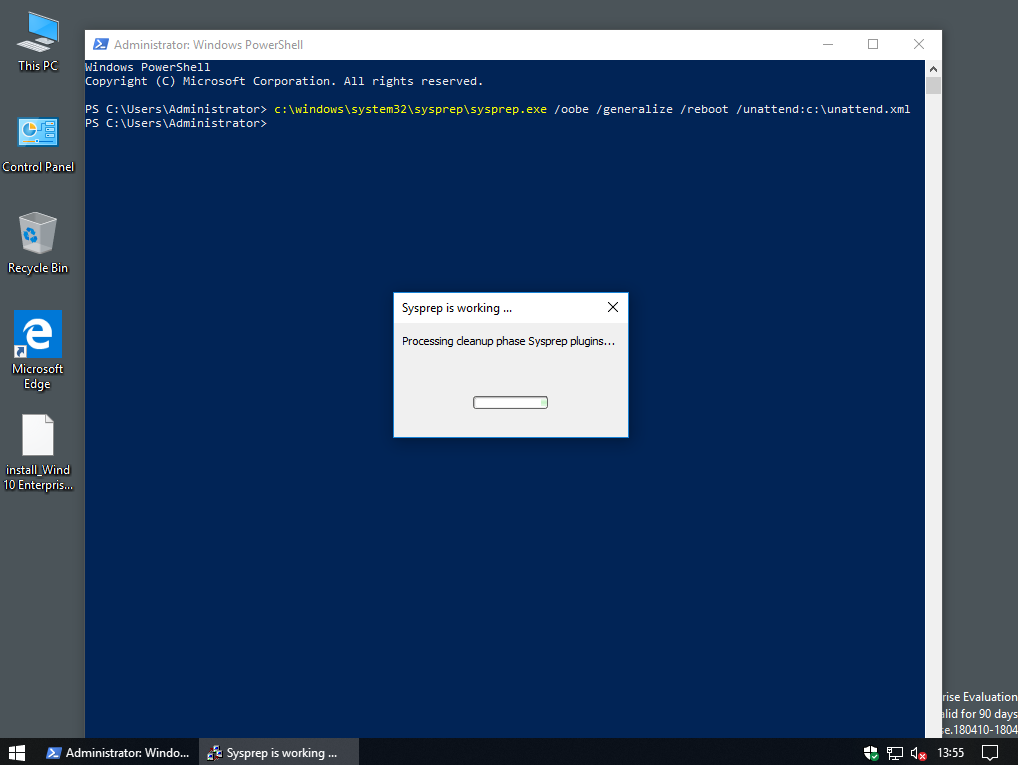
- If I skip the first few steps and only follow part 3 to create an unattend.xml file, place that in the sysprep folder on my vm. Sysprep with generalize and oobe and shut down, take a snapshot, then save the image to a usb drive with clonezilla, would I then be able to restore that image to workstations and have it skip through oobe?
- Resources for IT Professionals Sign in. United States (English).
This guide describes how to deploy Acrobat DC via App-V so that the application is delivered on demand but runs as if installed locally. For a deployment overview, refer to the App-V deployment video.
Downloads:
DC/Continuous track:
App-V Kit (updated May, 2020): Adds support for Office versions O2016, O2019, and O365 as well as the PDFMaker Add-Ins for MS Word/Excel/PPT for Create PDF and Share PDF.
Classic track:
Unsupported scenarios¶
User-publish
Roaming profiles.
App-V is not tested in Citrix environments.

System requirements¶
Microsoft Application Virtualization Sequencer Version 5.0 SP3 or 5.1.
Acrobat (either track)
Products sequenced on a 32-bit machine must be deployed on 32-bit clients and products sequenced on a 64-bit machine must be deployed on 64-bit clients.
Tuning¶
Tune the installer prior to imaging and deployment.
Tuning helps mitigate performance issues, simplifies the end user experience, and allows you to disable features and behaviors that should not be accessible to end users in an IT-managed environment.
Accept the EULA on behalf of all users by using the PRTK tool.
If the product language should be different than the OS language, set the language.
Suppress registration (there are multiple ways: Wizard, cmd line property, PRTK tool).
Disable push notifications: Set
HKLMSOFTWAREWOW6432NodePoliciesAdobe(productname)(version)FeatureLockdowncServicesbToggleNotificationsto 0.Disable the Help > Repair Acrobat Installation menu by setting the following to 1 (DWORD):
32 bit machines:
[HKLMSOFTWAREAdobe(productname)(version)Installer]'DisableMaintainence'64 bit machines:
[HKLMSOFTWAREWow6432NodeAdobe(productname)(version)Installer]'DisableMaintainence'
Other settings
There are over 500 other registry preferences documented in the Preference Reference. Use the Wizard or manual/scripted methods to customer the product.
Preparing the environment¶
Prepare the sequencing machine following Microsoft’s guidelines.
Create the following registry DWORD entry with a value of 1 to see the option of selecting PVAD while sequencing:
[HKEY_LOCAL_MACHINESOFTWAREMicrosoftAppVSequencerCompatibility]EnablePVADControl=1Processes that normally run on your computer can slow down the sequencing process and cause irrelevant data to be gathered during sequencing. Because the Sequencer scans for these (and similar) processes before creating a Virtual Application Package, the following programs should be stopped:
Windows Defender
Antivirus software
Disk Defragmentation Software
Windows Search
Microsoft Update
Any open Windows Explorer session
Optional: Use the Customization Wizard to further customize the installer.
Creating an App-V Package¶
Create a template¶
Templates allow you to control what files become part of the package, and you should exclude unnecessary files. You may wish to create the template after sequencing as described below.
To create a template, start with the provided template, OR perform the following steps:
Launch the Microsoft App-V Sequencer.
Go to Tools > Options.
In the pop-up, go to Exclusion Items tab.
Choose New.
Add the following folders to the Exclusion Items List:
[{Profile}][{AppData}][{LocalAppDataLow}][{CommonAppData}]AdobeSLStore[{ProgramFilesCommonX86}]AdobePCF[{ProgramFilesCommonX86}]AdobeSLCache[{ProgramFilesCommonX86}]AdobeAdobePCD[{AppVPackageRoot}]AcrobatBrowsernppdf32
Close the options window.
Choose File > Save As Template…
Choose OK when the dialog appears.
Save as an
.appvtfile.Exit.
Sequence Adobe Acrobat¶
There are two ways to approach sequencing:
Use the Microsoft Sequencer UI, and create a template file after you create the package as described below. This method incorporates all the changes included the exclusion list as well as the configuration in the package editor’s advanced tab window.
Create the Acrobat App-V package with powershell command below. Doing so replaces steps 1-25 but does not incorporate the settings in the last steps. For example, for the DC track:
Manual steps
Start the Microsoft Sequencer.
Choose Go to File > Load Template… and select your saved template (
.appvt).Select Create a new Virtual Application Package > Create Package.
Choose Next.
If there are any warnings on the Prepare Computer screen, correct them.
Choose Next.
On the Type of Application screen, select Standard Application.
Choose Next.
On the Select Installer screen, enter the path to your product installation files (Setup.exe). For custom installs, check Perform Custom Installation.
Choose Next.
In the Package Name screen, enter an application name (such as Adobe Acrobat DC).
In the PVAD screen, enter the Acrobat installation path. Install Acrobat to this location only. For example,
C:ProgramFilesx86)AdobeAcrobatDCfor a DC install.When the installer appears in the Sequencer Screen, select “Trial and subscription mode”. Note: Licensing options appear in subsequent sections.
Install to the location that has been entered as PVAD above using the “Customize” button in the Installer.
Follow the on-screen instructions.
Choose Close (do not choose Launch Now). If you have chosen Custom Installation Option, nothing will happen on the machine.
To install Acrobat via a command-line and suppress the EULA:
Open a command window in admin mode.
Go to the Acrobat installer location.
Verify Acrobat is installed in the PVAD location.
Run the following:
Create a new registry preference (Serialized installs only-all tracks):
18a. Named User Licensing installs only. Create the following two keys:
18b. Feature Restricted Licensing connected and offline packages. Create the following key:
After installation completes, select I am finished installing.
Choose Next.
Do not run any Application in the Configure Software screen. Choose Next.
After the Sequencer collects the system changes, review the Installation Report which detects common sequencing issues.
Choose Next.
Choose Stop Now.
Choose Next.
Select “Continue to modify package without Saving using the package editor”.
Choose Next.
In Package Editor window, open the Advanced Tab and check the following checkboxes:
Allow virtual applications full write access to virtual file system.
Allow COM Objects to interact with Local System.
Allow all named objects to interact with Local System.
Verify the files and folders excluded above do not appear in the package:
<Packageroot>AcrobatBrowser>nppdf32.*(any files starting with that string)<Packageroot>VFSProfile<Packageroot>VFSLocalAppDataLow<Packageroot>VFSAppData<Packageroot>VFSCommonAppdataAdobeSLStore<Packageroot>VFSProgramFilesCommonX86AdobeSLCache<Packageroot>VFSProgramFilesCommonX86AdobeAdobePCD<Packageroot>VFSProgramFilesCommonX86AdobePCF
Select “Merge with local Directory” option for the following folders.
<Packageroot>VFSProgramFilesCommonX86Adobe<Packageroot>VFSCommonAppdataAdobe
Add the necessary files to the Scripts folder.
C:ProgramFiles(x86)CommonFilesAdobeOOBEPDAppP7dispatchtable.xml(Available on the sequencer machine)adobe_prtk.exe(Available as part of APTEE as a download from https://download.macromedia.com/pub/developer/prtk/Adobe_Provisioning_Toolkit_10_0_ALL.exe.
31a. Feature Restricted Licensing connected and offline packages only.
Go to https://adminconsole.adobe.com/
Create a license only package. (Do NOT include the Acrobat installer in the package).
Add adobe-licensing-toolkit.exe and json files from the FRL package created above to the scripts folder.
Embed scripts¶
Download and unzip required scripts.
Go to the Package Files Tab in the Editor.
Navigate to Package > Scripts.
Right-Click the Scripts folder and choose Add to embed a new script into the package so that they can be leveraged on the client machine.
Publish.ps1: A PowerShell script to identify the location of App-V Acrobat on system, deploy Acrobat App-V in various Licensing modes, and suppress the updater on the client.
Unpublish.ps1: An un-publish script which removes Adobe Acrobat activation as well as the updater and the location entry created by Publish.ps1.
To volume serialize Acrobat on the client machine, include prov.xml in the package scripts. Generate this XML File on the sequencer machine using adobe_prtk.exe, and then run the APTEE Command from an elevated command prompt as shown below.
Runtime.bat: This run-time script is only required when Acrobat should run in sandbox mode. The script creates the parent registry of the pass-through entries in App-V. This script only works for the domain users and will throw error 534 if a local user tries to open the Virtual DC App. Use the above script only when the package is published to the domain users.
Note
NUL (named user) installs don’t require using prov.xml.
Save the package.
Close the editor.
Post sequencing steps¶
The DeploymentConfig.xml file resides in the same folder as the .appv file. Modify it as described below.
Create script extension points by adding the script calls inside the
<MachineScripts>tag. The Publish and Unpublish scripts require arguments as follows:Channel name: Either
2020|2017|2015|DC.The Package ID: Copy it from the
<DeploymentConfigurationline. For example,PackageId='dcc25ced-6e2e-4a44-8ef3-4afe3e3fbde8'Product path: Copy it from the
<ApplicationIdline in the<Applications>tag. For example,<ApplicationId='[{AppVPackageRoot}]AcrobatAcrobat.exe'Enabled='true'>
Note
NUL installs should remove [-Serialize]</Arguments> from the example below.
Note
the Publish script takes -Serialize as an optional argument to volume serialize the product. Otherwise, Acrobat is deployed in trial mode on the client machine.
Set the COM integration mode:
Set named object interaction. Change all <Objects> tags to false:
Configure <UserScripts> to add Runtime.bat so that it is triggered on the creation of the virtual environment for the package.
Disable virtual fonts subsystem. The required fonts would be locally registered on the client machine by our supplementary App-V installer.
(OPTIONAL) Hide unnecessary extension points. Configure <Applications> to hide “AcrobatInfo” application from being seen in the list of recommended programs when users try to change the default PDF viewer. This application also has the name “Adobe Acrobat”; however, as a default application for .pdf files, it does not perform anything and so should not appear.
Feature Restricted Licensing connected or offline package.
Go to https://adminconsole.adobe.com/
Create a license only package. (Do NOT include the Acrobat installer in the package).
Add adobe-licensing-toolkit.exe and json files from the FRL package created above to the scripts folder.
Add the
-Frloption to the machine scripts tag:
Deploying a client package¶
Prerequisites¶
Enable scripting on client machines. The Acrobat Package contains scripts which are executed on the client machine in order to provide a feature rich experience to the end user. The scripts can be enabled via:
Publish the package globally: Extension points for the Acrobat App-V Package require machine-level installation. With App-V 5.0 SP2, publishing globally automatically creates these extensions and Acrobat behaves like an installed application.
Note
User-publish is not supported.
Apply the hotfix to the App-V 5.0 SP3 Client See https://support.microsoft.com/kb/3039022. This hot-fix fixes the problems of the application crashing while performing an OCR, editing a PDF file and opening a shared review PDF file.
Optional: Enable FeatureLockdown on Clients. To suppress or lock certain features on the client, do one of the following:
Manually create the FeatureLockDown keys on the client machine either by pushing policies from the server.
Add the keys inside the package itself from the package editor window using the Registry tab. This requires removing the
HKEY_LOCAL_MACHINESOFTWAREPoliciesregistry entry from the list of pass-through registry keys (atHKEY_LOCAL_MACHINESOFTWAREMicrosoftAppVSubsystemVirtualRegistryon the client machine. Since, the change is machine specific this will impact other virtual applications as well, hence, care must be taken while choosing this step.
Publishing¶
What Is Oobe Create Elevated Object Server
To publish the package globally, run the following Power-Shell command:
To leverage all of Acrobat’s features, install the supplementary App-V Kit downloads (at the top of this page) on the user’s machine. The kit does the following:
MS Office Integration - Context Menu and In-App Acrobat Ribbons.
Mail Integration - MS Outlook and Lotus Notes will start showing Acrobat Features.
Adobe PDF Printer - Allows the user to print any file to Adobe PDF.
Web Capture - Allows the user to be able to convert a webpage to Adobe PDF inside the Browser.
Registers necessary fonts on the client which will be used by the virtual application.
Unpublishing¶
If you have installed the MSI at the time of publishing the package, then it is recommended to uninstall it before unpublishing or removing the package from your system. Since the Acrobat Package creates extension points on system, it is necessary to stop the package before unpublishing and removing it from the client machine. The package should be unpublished globally as follows:
User Oobe Create Elevated Object Server Autopilot
Stop the package.
Verify
adobe_prtk.exeis in the same directory as the package.Run the following:
Tip
If you unpublish the App-V package from the machine instance on user logout, then users won’t need to manually sign out in order to avoid over activation messages on subsequent log-ins.
Patching Acrobat¶
Note
Due to a number of significant changes, it is not possible to update existing installs with the August, 2020 update. When migrating to a post-August, 2020 release, create a new package with a full installer.
Prerequisites¶
An existing Acrobat App-V Package
The installer from which the actual Acrobat Package was created.
The latest Acrobat patch or update of the same channel from which the original package was created.
The template that was created in the “Create a template” section above.
Close the same processes that were closed when publishing the initial package.
Registry settings are not migrated during a patch. If required, copy existing registries to the new install.
Pre-sequencing steps¶
The pre-sequencing steps are identical to those for creating an App-V Package.
Sequencing a patch¶
Start the Microsoft Sequencer.
Choose File > Load Template… and select your saved template (
.appvt).Choose Modify Existing Virtual Application Package. A dialog appears.
Choose Update Application in existing package.
Choose Next.
Browse to the .appv file of the virtual application package that needs to be patched.
Choose Next.
After the sequencer is done loading the package, it will display the issues if anything is wrong with the machine. If there are no serious issues, choose Next. If there are issues, address those issues and repeat the previous steps.
Choose Select the installer for the application.
Browse to the
.msppatch file.Choose Next. The patch is invoked automatically.
If the Windows installer asks for the location of the MSI file, point to the location where the application installer was copied.
Choose OK.
After the patch completes, close the patch installer.
Create a new registry preference (for products released after December, 2018):
After installation, select I am finished installing.
Choose Next.
After the application collects the system changes, choose Next.
Review the Installation Report which detects common sequencing issues during sequencing.
Click Next.
Do not go to Configure Screen. Instead, select Stop Now.
Choose Next.
Select Continue to modify package without Saving using the package editor.
Choose Next.
Choose Close. The Package Editor will open.
Move to Advanced Tab and check the following:
Allow virtual applications full write access to virtual file system.
Allow COM Objects to interact with Local System.
Allow all named objects to interact with Local System.
Verify the files excluded from the package (above) are not present inside the package.
Select “Merge with local Directory” option for the following folders.
<Packageroot>VFSProgramFilesCommonX86Adobe<Packageroot>VFSCommonAppdataAdobe
The scripts and other files added while creating the package from scratch are lost during patching. Re-add them as described in “Sequence Adobe Acrobat” above.
Save the package and move on to Post Sequencing Steps in the following section.
Post Sequencing Steps¶
Modify DeploymentConfig.xml as described above.
Known issues¶
Automatic updates or manual end user updates are not supported. App-V updates are pushed by enterprise IT.
On-the-fly switching of the default PDF handler (viewer) from within the application is not supported. Handler selection can occur at install time or prior to deployment.
PDF previews are not visible in Windows Explorer.
Opening a PDF inside Internet Explorer does not work on Win 8.1 and Win 10 when IE’s Enhanced Protected Mode is turned on.
Conversion of .vsl files does not work with App-V Acrobat via Context Menu Handlers. For details and a workaround, see https://helpx.adobe.com/acrobat/kb/pdf-conversion-of-visio-files-through-context-menu-in-app-v-envi.html
App-V Acrobat may crash when invoking Send for Signature if App-V Reader is present on the same machine and not previously launched by the user. For details, see https://helpx.adobe.com/acrobat/kb/send-for-signature-crashes.html.
Known issues added June, 2020¶
NUL-license is not deactivated from the machine on AppV package unpublish.
Thumbnails for non-PDF files are missing while creating and combinig portfolios. There is no current workaround.
The Office PDFMaker Add-In is not enabled on installation. The add-in must be enabled manually from MS Word/PPT/Excel. To do so:
Launch MS Word/Excel/PPT
Click on Options from the bottom left corner
Click on “Add-Ins” from the Options menu
Select “COM Add-ins” and Click “Go” from bottom of the menu
Enable checkbox for “Acrobat PDFMaker Office COM Addin”.
Click OK.
The Acrobat tab will now appear on the MS Office app so that users can create and share PDFs.
A registry entry is not added/updated/removed during the install and uninstall of Acrobat and context menu therefore fail to function. To enable the Create and Combine menu items in the context menu, do the following:
Create a new key:
HKLMSOFTWAREWOW6432NodeAdobeAcrobatElements{Track–DC/2015/2017}InstallPathSet the value to:
Default|C:ProgramDataMicrosoftAppVClientIntegration{PackageID}RootAcrobatElements
Applies to: Windows 10, Windows 8.1, Windows 8, Windows 7, Windows Server 2019, Windows Server 2016, Windows Server (Semi-annual Channel), Windows Server 2012 R2, Windows Server 2012, Windows Server 2008 R2
This topic describes how to use Windows Server to deploy Roaming User Profiles to Windows client computers. Roaming User Profiles redirects user profiles to a file share so that users receive the same operating system and application settings on multiple computers.
For a list of recent changes to this topic, see the Change history section of this topic.
Important
Due to the security changes made in MS16-072, we updated Step 4: Optionally create a GPO for Roaming User Profiles in this topic so that Windows can properly apply the Roaming User Profiles policy (and not revert to local policies on affected PCs).
Important
User customizations to Start is lost after an OS in-place upgrade in the following configuration:
- Users are configured for a roaming profile
- Users are allowed to make changes to Start
As a result, the Start menu is reset to the default of the new OS version after the OS in-place upgrade. For workarounds, see Appendix C: Working around reset Start menu layouts after upgrades.
Prerequisites
Hardware requirements
Roaming User Profiles requires an x64-based or x86-based computer; it isn't supported by Windows RT.
Software requirements
Roaming User Profiles has the following software requirements:
If you are deploying Roaming User Profiles with Folder Redirection in an environment with existing local user profiles, deploy Folder Redirection before Roaming User Profiles to minimize the size of roaming profiles. After the existing user folders have been successfully redirected, you can deploy Roaming User Profiles.
To administer Roaming User Profiles, you must be signed in as a member of the Domain Administrators security group, the Enterprise Administrators security group, or the Group Policy Creator Owners security group.
Client computers must run Windows 10, Windows 8.1, Windows 8, Windows 7, Windows Vista, Windows Server 2012 R2, Windows Server 2012, Windows Server 2008 R2, or Windows Server 2008.
Client computers must be joined to the Active Directory Domain Services (AD DS) that you are managing.
A computer must be available with Group Policy Management and Active Directory Administration Center installed.
A file server must be available to host roaming user profiles.
- If the file share uses DFS Namespaces, the DFS folders (links) must have a single target to prevent users from making conflicting edits on different servers.
- If the file share uses DFS Replication to replicate the contents with another server, users must be able to access only the source server to prevent users from making conflicting edits on different servers.
- If the file share is clustered, disable continuous availability on the file share to avoid performance issues.
To use primary computer support in Roaming User Profiles, there are additional client computer and Active Directory schema requirements. For more information, see Deploy Primary Computers for Folder Redirection and Roaming User Profiles.
The layout of a user's Start menu won't roam on Windows 10, Windows Server 2019, or Windows Server 2016 if they're using more than one PC, Remote Desktop Session Host, or Virtualized Desktop Infrastructure (VDI) server. As a workaround, you can specify a Start layout as described in this topic. Or you can make use of user profile disks, which properly roam Start menu settings when used with Remote Desktop Session Host servers or VDI servers. For more info, see Easier User Data Management with User Profile Disks in Windows Server 2012.
Considerations when using Roaming User Profiles on multiple versions of Windows
If you decide to use Roaming User Profiles across multiple versions of Windows, we recommend taking the following actions:
- Configure Windows to maintain separate profile versions for each operating system version. This helps prevent undesirable and unpredictable issues such as profile corruption.
- Use Folder Redirection to store user files such as documents and pictures outside of user profiles. This enables the same files to be available to users across operating system versions. It also keeps profiles small and sign-ins quick.
- Allocate sufficient storage for Roaming User Profiles. If you support two operating system versions, profiles will double in number (and thus total space consumed) because a separate profile is maintained for each operating system version.
- Don't use Roaming User Profiles across computers running Windows Vista/Windows Server 2008 and Windows 7/Windows Server 2008 R2. Roaming between these operating system versions isn't supported due to incompatibilities in their profile versions.
- Inform your users that changes made on one operating system version won't roam to another operating system version.
- When moving your environment to a version of Windows that uses a different profile version (such as from Windows 10 to Windows 10, version 1607—see Appendix B: Profile version reference information for a list), users receive a new, empty roaming user profile. You can minimize the impact of getting a new profile by using Folder Redirection to redirect common folders. There isn't a supported method of migrating roaming user profiles from one profile version to another.
Step 1: Enable the use of separate profile versions
If you are deploying Roaming User Profiles on computers running Windows 8.1, Windows 8, Windows Server 2012 R2, or Windows Server 2012, we recommend making a couple of changes to your Windows environment prior to deploying. These changes help ensure that future operating system upgrades go smoothly, and facilitate the ability to simultaneously run multiple versions of Windows with Roaming User Profiles.
To make these changes, use the following procedure.
Download and install the appropriate software update on all computers on which you're going to use roaming, mandatory, super-mandatory, or domain default profiles:
- Windows 8.1, or Windows Server 2012 R2: install the software update described in article 2887595 in the Microsoft Knowledge Base (when released).
- Windows 8 or Windows Server 2012: install the software update described in article 2887239 in the Microsoft Knowledge Base.
On all computers running Windows 8.1, Windows 8, Windows Server 2012 R2, or Windows Server 2012 on which you will use Roaming User Profiles, use Registry Editor or Group Policy to create the following registry key DWORD Value and set it to
1. For information about creating registry keys by using Group Policy, see Configure a Registry Item.Warning
Incorrectly editing the registry may severely damage your system. Before making changes to the registry, you should back up any valued data on the computer.
Restart the computers.
Step 2: Create a Roaming User Profiles security group
If your environment is not already set up with Roaming User Profiles, the first step is to create a security group that contains all users and/or computers to which you want to apply Roaming User Profiles policy settings.
- Administrators of general-purpose roaming user profiles deployments typically create a security group for users.
- Administrators of Remote Desktop Services or virtualized desktop deployments typically use a security group for users and the shared computers.
Here's how to create a security group for Roaming User Profiles:
Open Server Manager on a computer with Active Directory Administration Center installed.
On the Tools menu, select Active Directory Administration Center. Active Directory Administration Center appears.
Right-click the appropriate domain or OU, select New, and then select Group.
In the Create Group window, in the Group section, specify the following settings:
- In Group name, type the name of the security group, for example: Roaming User Profiles Users and Computers.
- In Group scope, select Security, and then select Global.
In the Members section, select Add. The Select Users, Contacts, Computers, Service Accounts or Groups dialog box appears.
If you want to include computer accounts in the security group, select Object Types, select the Computers check box and then select OK.
Type the names of the users, groups, and/or computers to which you want to deploy Roaming User Profiles, select OK, and then select OK again.
Step 3: Create a file share for roaming user profiles
If you do not already have a separate file share for roaming user profiles (independent from any shares for redirected folders to prevent inadvertent caching of the roaming profile folder), use the following procedure to create a file share on a server running Windows Server.
Note
Some functionality might differ or be unavailable depending on the version of Windows Server you're using.
Here's how to create a file share on Windows Server:
In the Server Manager navigation pane, select File and Storage Services, and then select Shares to display the Shares page.
In the Shares tile, select Tasks, and then select New Share. The New Share Wizard appears.
On the Select Profile page, select SMB Share – Quick. If you have File Server Resource Manager installed and are using folder management properties, instead select SMB Share - Advanced.
On the Share Location page, select the server and volume on which you want to create the share.
On the Share Name page, type a name for the share (for example, User Profiles$) in the Share name box.
Tip
When creating the share, hide the share by putting a
$after the share name. This hides the share from casual browsers.On the Other Settings page, clear the Enable continuous availability checkbox, if present, and optionally select the Enable access-based enumeration and Encrypt data access checkboxes.
On the Permissions page, select Customize permissions…. The Advanced Security Settings dialog box appears.
Select Disable inheritance, and then select Convert inherited permissions into explicit permission on this object.
Set the permissions as described in Required permissions for the file share hosting roaming user profiles and shown in the following screen shot, removing permissions for unlisted groups and accounts, and adding special permissions to the Roaming User Profiles Users and Computers group that you created in Step 1.
Figure 1 Setting the permissions for the roaming user profiles share
If you chose the SMB Share - Advanced profile, on the Management Properties page, select the User Files Folder Usage value.
If you chose the SMB Share - Advanced profile, on the Quota page, optionally select a quota to apply to users of the share.
On the Confirmation page, select Create.
Required permissions for the file share hosting roaming user profiles
| User Account | Access | Applies to |
|---|---|---|
| System | Full control | This folder, subfolders and files |
| Administrators | Full Control | This folder only |
| Creator/Owner | Full Control | Subfolders and files only |
| Security group of users needing to put data on share (Roaming User Profiles Users and Computers) | List folder / read data (Advanced permissions) Create folders / append data (Advanced permissions) | This folder only |
| Other groups and accounts | None (remove) |
Step 4: Optionally create a GPO for Roaming User Profiles
If you do not already have a GPO created for Roaming User Profiles settings, use the following procedure to create an empty GPO for use with Roaming User Profiles. This GPO allows you to configure Roaming User Profiles settings (such as primary computer support, which is discussed separately), and can also be used to enable Roaming User Profiles on computers, as is typically done when deploying in virtualized desktop environments or with Remote Desktop Services.
Here's how to create a GPO for Roaming User Profiles:
Open Server Manager on a computer with Group Policy Management installed.
From the Tools menu select Group Policy Management. Group Policy Management appears.
Right-click the domain or OU in which you want to setup Roaming User Profiles, then select Create a GPO in this domain, and Link it here.
In the New GPO dialog box, type a name for the GPO (for example, Roaming User Profile Settings), and then select OK.
Right-click the newly created GPO and then clear the Link Enabled checkbox. This prevents the GPO from being applied until you finish configuring it.
Select the GPO. In the Security Filtering section of the Scope tab, select Authenticated Users, and then select Remove to prevent the GPO from being applied to everyone.
In the Security Filtering section, select Add.
In the Select User, Computer, or Group dialog box, type the name of the security group you created in Step 1 (for example, Roaming User Profiles Users and Computers), and then select OK.
Select the Delegation tab, select Add, type Authenticated Users, select OK, and then select OK again to accept the default Read permissions.
This step is necessary due to security changes made in MS16-072.
Important
Due to the security changes made in MS16-072A, you now must give the Authenticated Users group delegated Read permissions to the GPO - otherwise the GPO won't get applied to users, or if it's already applied, the GPO is removed, redirecting user profiles back to the local PC. For more info, see Deploying Group Policy Security Update MS16-072.
Step 5: Optionally set up Roaming User Profiles on user accounts
If you are deploying Roaming User Profiles to user accounts, use the following procedure to specify roaming user profiles for user accounts in Active Directory Domain Services. If you are deploying Roaming User Profiles to computers, as is typically done for Remote Desktop Services or virtualized desktop deployments, instead use the procedure documented in Step 6: Optionally set up Roaming User Profiles on computers.
Note
If you set up Roaming User Profiles on user accounts by using Active Directory and on computers by using Group Policy, the computer-based policy setting takes precedence.
Here's how to set up Roaming User Profiles on user accounts:
In Active Directory Administration Center, navigate to the Users container (or OU) in the appropriate domain.
Select all users to which you want to assign a roaming user profile, right-click the users and then select Properties.
In the Profile section, select the Profile path: checkbox and then enter the path to the file share where you want to store the user's roaming user profile, followed by
%username%(which is automatically replaced with the user name the first time the user signs in). For example:fs1.corp.contoso.comUser Profiles$%username%To specify a mandatory roaming user profile, specify the path to the NTuser.man file that you created previously, for example,
fs1.corp.contoso.comUser Profiles$default. For more information, see Create mandatory user profiles.Select OK.
Note
By default, deployment of all Windows® Runtime-based (Windows Store) apps is allowed when using Roaming User Profiles. However, when using a special profile, apps are not deployed by default. Special profiles are user profiles where changes are discarded after the user signs out:
To remove restrictions on app deployment for special profiles, enable the Allow deployment operations in special profiles policy setting (located in Computer ConfigurationPoliciesAdministrative TemplatesWindows ComponentsApp Package Deployment). However, deployed apps in this scenario will leave some data stored on the computer, which could accumulate, for example, if there are hundreds of users of a single computer. To clean up apps, locate or develop a tool that uses the CleanupPackageForUserAsync API to clean up app packages for users who no longer have a profile on the computer.
For additional background information about Windows Store apps, see Manage Client Access to the Windows Store.
Step 6: Optionally set up Roaming User Profiles on computers
If you are deploying Roaming User Profiles to computers, as is typically done for Remote Desktop Services or virtualized desktop deployments, use the following procedure. If you are deploying Roaming User Profiles to user accounts, instead use the procedure described in Step 5: Optionally set up Roaming User Profiles on user accounts.
You can use Group Policy to apply Roaming User Profiles to computers running Windows 8.1, Windows 8, Windows 7, Windows Vista, Windows Server 2019, Windows Server 2016, Windows Server 2012 R2, Windows Server 2012, Windows Server 2008 R2, or Windows Server 2008.
Note
If you set up Roaming User Profiles on computers by using Group Policy and on user accounts by using Active Directory, the computer-based policy setting takes precedence.
Here's how to set up Roaming User Profiles on computers:
Open Server Manager on a computer with Group Policy Management installed.
From the Tools menu, select Group Policy Management. Group Policy Management will appear.
In Group Policy Management, right-click the GPO you created in Step 3 (for example, Roaming User Profiles Settings), and then select Edit.
In the Group Policy Management Editor window, navigate to Computer Configuration, then Policies, then Administrative Templates, then System, and then User Profiles.
Right-click Set roaming profile path for all users logging onto this computer and then select Edit.
Tip
A user's home folder, if configured, is the default folder used by some programs such as Windows PowerShell. You can configure an alternative local or network location on a per-user basis by using the Home folder section of the user account properties in AD DS. To configure the home folder location for all users of a computer running Windows 8.1, Windows 8, Windows Server 2019, Windows Server 2016, Windows Server 2012 R2, or Windows Server 2012 in a virtual desktop environment, enable the Set user home folder policy setting, and then specify the file share and drive letter to map (or specify a local folder). Do not use environment variables or ellipses. The user's alias is appended to the end of the path specified during user sign on.
In the Properties dialog box, select Enabled
In the Users logging onto this computer should use this roaming profile path box, enter the path to the file share where you want to store the user's roaming user profile, followed by
%username%(which is automatically replaced with the user name the first time the user signs in). For example:fs1.corp.contoso.comUser Profiles$%username%To specify a mandatory roaming user profile, which is a preconfigured profile to which users cannot make permanent changes (changes are reset when the user signs out), specify the path to the NTuser.man file that you created previously, for example,
fs1.corp.contoso.comUser Profiles$default. For more information, see Creating a Mandatory User Profile.Select OK.
Step 7: Optionally specify a Start layout for Windows 10 PCs
You can use Group Policy to apply a specific Start menu layout so that users see the same Start layout on all PCs. If users sign in to more than one PC and you want them to have a consistent Start layout across PCs, make sure that the GPO applies to all of their PCs.
To specify a Start layout, do the following:
- Update your Windows 10 PCs to Windows 10 version 1607 (also known as the Anniversary Update) or newer, and install the March 14th, 2017 cumulative update (KB4013429) or newer.
- Create a full or partial Start menu layout XML file. To do so, see Customize and export Start layout.
- If you specify a full Start layout, a user can't customize any part of the Start menu. If you specify a partial Start layout, users can customize everything but the locked groups of tiles you specify. However, with a partial Start layout, user customizations to the Start menu won't roam to other PCs.
- Use Group Policy to apply the customized Start layout to the GPO you created for Roaming User Profiles. To do so, see Use Group Policy to apply a customized Start layout in a domain.
- Use Group Policy to set the following registry value on your Windows 10 PCs. To do so, see Configure a Registry Item.
| Action | Update |
|---|---|
| Hive | HKEY_LOCAL_MACHINE |
| Key path | SoftwareMicrosoftWindowsCurrentVersionExplorer |
| Value name | SpecialRoamingOverrideAllowed |
| Value type | REG_DWORD |
| Value data | 1 (or 0 to disable) |
| Base | Decimal |
- (Optional) Enable first-time logon optimizations to make signing in faster for users. To do so, see Apply policies to improve sign-in time.
- (Optional) Further decrease sign-in times by removing unnecessary apps from the Windows 10 base image you use to deploy client PCs. Windows Server 2019 and Windows Server 2016 don't have any pre-provisioned apps, so you can skip this step on server images.
To remove apps, use the Remove-AppxProvisionedPackage cmdlet in Windows PowerShell to uninstall the following applications. If your PCs are already deployed you can script the removal of these apps using the Remove-AppxPackage.
- Microsoft.windowscommunicationsapps_8wekyb3d8bbwe
- Microsoft.BingWeather_8wekyb3d8bbwe
- Microsoft.DesktopAppInstaller_8wekyb3d8bbwe
- Microsoft.Getstarted_8wekyb3d8bbwe
- Microsoft.Windows.Photos_8wekyb3d8bbwe
- Microsoft.WindowsCamera_8wekyb3d8bbwe
- Microsoft.WindowsFeedbackHub_8wekyb3d8bbwe
- Microsoft.WindowsStore_8wekyb3d8bbwe
- Microsoft.XboxApp_8wekyb3d8bbwe
- Microsoft.XboxIdentityProvider_8wekyb3d8bbwe
- Microsoft.ZuneMusic_8wekyb3d8bbwe
Note
Uninstalling these apps decreases sign-in times, but you can leave them installed if your deployment needs any of them.
Step 8: Enable the Roaming User Profiles GPO
If you set up Roaming User Profiles on computers by using Group Policy, or if you customized other Roaming User Profiles settings by using Group Policy, the next step is to enable the GPO, permitting it to be applied to affected users.
Tip

If you plan to implement primary computer support, do so now, before you enable the GPO. This prevents user data from being copied to non-primary computers before primary computer support is enabled. For the specific policy settings, see Deploy Primary Computers for Folder Redirection and Roaming User Profiles.
Here's how to enable the Roaming User Profile GPO:
- Open Group Policy Management.
- Right-click the GPO that you created and then select Link Enabled. A checkbox appears next to the menu item.
Step 9: Test Roaming User Profiles
To test Roaming User Profiles, sign in to a computer with a user account configured for Roaming User Profiles, or sign in to a computer configured for Roaming User Profiles. Then confirm that the profile is redirected.
Here's how to test Roaming User Profiles:
Sign in to a primary computer (if you enabled primary computer support) with a user account for which you have enabled Roaming User Profiles enabled. If you enabled Roaming User Profiles on specific computers, sign in to one of these computers.
If the user has previously signed in to the computer, open an elevated command prompt, and then type the following command to ensure that the latest Group Policy settings are applied to the client computer:
To confirm that the user profile is roaming, open Control Panel, select System and Security, select System, select Advanced System Settings, select Settings in the User Profiles section and then look for Roaming in the Type column.
Appendix A: Checklist for deploying Roaming User Profiles
| Status | Action |
|---|---|
| ☐ ☐ ☐ ☐ ☐ | 1. Prepare domain - Join computers to domain - Enable the use of separate profile versions - Create user accounts - (Optional) Deploy Folder Redirection |
| ☐ | 2. Create security group for Roaming User Profiles - Group name: - Members: |
| ☐ | 3. Create a file share for Roaming User Profiles - File share name: |
| ☐ | 4. Create a GPO for Roaming User Profiles - GPO name: |
| ☐ | 5. Configure Roaming User Profiles policy settings |
| ☐ ☐ ☐ | 6. Enable Roaming User Profiles - Enabled in AD DS on user accounts? - Enabled in Group Policy on computer accounts? |
| ☐ | 7. (Optional) Specify a mandatory Start layout for Windows 10 PCs |
| ☐ ☐ ☐ ☐ | 8. (Optional) Enable primary computer support - Designate primary computers for users - Location of user and primary computer mappings: - (Optional) Enable primary computer support for Folder Redirection - Computer-based or User-based? - (Optional) Enable primary computer support for Roaming User Profiles |
| ☐ | 9. Enable the Roaming User Profiles GPO |
| ☐ | 10. Test Roaming User Profiles |
Appendix B: Profile version reference information
Each profile has a profile version that corresponds roughly to the version of Windows on which the profile is used. For example, Windows 10, version 1703 and version 1607 both use the .V6 profile version. Microsoft creates a new profile version only when necessary to maintain compatibility, which is why not every version of Windows includes a new profile version.
The following table lists the location of Roaming User Profiles on various versions of Windows.
| Operating system version | Roaming User Profile location |
|---|---|
| Windows XP and Windows Server 2003 | <servername><fileshare><username> |
| Windows Vista and Windows Server 2008 | <servername><fileshare><username>.V2 |
| Windows 7 and Windows Server 2008 R2 | <servername><fileshare><username>.V2 |
| Windows 8 and Windows Server 2012 | <servername><fileshare><username>.V3 (after the software update and registry key are applied)<servername><fileshare><username>.V2 (before the software update and registry key are applied) |
| Windows 8.1 and Windows Server 2012 R2 | <servername><fileshare><username>.V4 (after the software update and registry key are applied)<servername><fileshare><username>.V2 (before the software update and registry key are applied) |
| Windows 10 | <servername><fileshare><username>.V5 |
| Windows 10, version 1703 and version 1607 | <servername><fileshare><username>.V6 |
Appendix C: Working around reset Start menu layouts after upgrades
Here are some ways to work around Start menu layouts getting reset after an in-place upgrade:
If only one user ever uses the device and the IT Admin uses a managed OS deployment strategy such as Configuration Manager they can do the following:
Export the Start menu layout with Export-Startlayout before the upgrade
Import the Start menu layout with Import-StartLayout after OOBE but before the user signs in
Note
Importing a StartLayout modifies the Default User profile. All user profiles created after the import has occurred will get the imported Start-Layout.
IT Admins can opt to manage Start's Layout with Group Policy. Using Group Policy provides a centralized management solution to apply a standardized Start Layout to users. There are 2 modes to modes to using Group Policy for Start management. Full Lockdown and Partial Lockdown. The full lockdown scenario prevents the user from making any changes to Start's layout. The partial lockdown scenario allows user to make changes to a specific area of Start. For more info, see Customize and export Start layout.
Note
User made changes in the partial lockdown scenario will still be lost during upgrade.
Let the Start layout reset occur and allow end users to reconfigure Start. A notification email or other notification can be sent to end users to expect their Start layouts to be reset after the OS upgrade to minimized impact.
Change history
The following table summarizes some of the most important changes to this topic.
| Date | Description | Reason |
|---|---|---|
| May 1st, 2019 | Added updates for Windows Server 2019 | |
| April 10th, 2018 | Added discussion of when user customizations to Start are lost after an OS in-place upgrade | Callout known issue. |
| March 13th, 2018 | Updated for Windows Server 2016 | Moved out of Previous Versions library and updated for current version of Windows Server. |
| April 13th, 2017 | Added profile information for Windows 10, version 1703, and clarified how roaming profile versions work when upgrading operating systems—see Considerations when using Roaming User Profiles on multiple versions of Windows. | Customer feedback. |
| March 14th, 2017 | Added optional step for specifying a mandatory Start layout for Windows 10 PCs in Appendix A: Checklist for deploying Roaming User Profiles. | Feature changes in latest Windows update. |
| January 23rd, 2017 | Added a step to Step 4: Optionally create a GPO for Roaming User Profiles to delegate Read permissions to Authenticated Users, which is now required because of a Group Policy security update. | Security changes to Group Policy processing. |
| December 29th, 2016 | Added a link in Step 8: Enable the Roaming User Profiles GPO to make it easier to get info on how to set Group Policy for primary computers. Also fixed a couple references to steps 5 and 6 that had the numbers wrong. | Customer feedback. |
| December 5th, 2016 | Added info explaining a Start menu settings roaming issue. | Customer feedback. |
| July 6th, 2016 | Added Windows 10 profile version suffixes in Appendix B: Profile version reference information. Also removed Windows XP and Windows Server 2003 from the list of supported operating systems. | Updates for the new versions of Windows, and removed info about versions of Windows that are no longer supported. |
| July 7th, 2015 | Added requirement and step to disable continuous availability when using a clustered file server. | Clustered file shares have better performance for small writes (which are typical with roaming user profiles) when continuous availability is disabled. |
| March 19th, 2014 | Capitalized profile version suffixes (.V2, .V3, .V4) in Appendix B: Profile version reference information. | Although Windows is case insensitive, if you use NFS with the file share, it's important to have the correct (uppercase) capitalization for the profile suffix. |
| October 9th, 2013 | Revised for Windows Server 2012 R2 and Windows 8.1, clarified a few things, and added the Considerations when using Roaming User Profiles on multiple versions of Windows and Appendix B: Profile version reference information sections. | Updates for new version; customer feedback. |